Talking Testing Tools
Without question, information security is a subject area that is not easy to grasp and readily understood. The breath of the subject is extensive yet detailed in its content, and while there is a significant amount of data available on the Internet, finding the right solution is not usually simple. One common security subject that many organizations would need to address is that of network testing i.e. technical checks to determine if networks, systems and software applications are protected from unauthorized hackers?
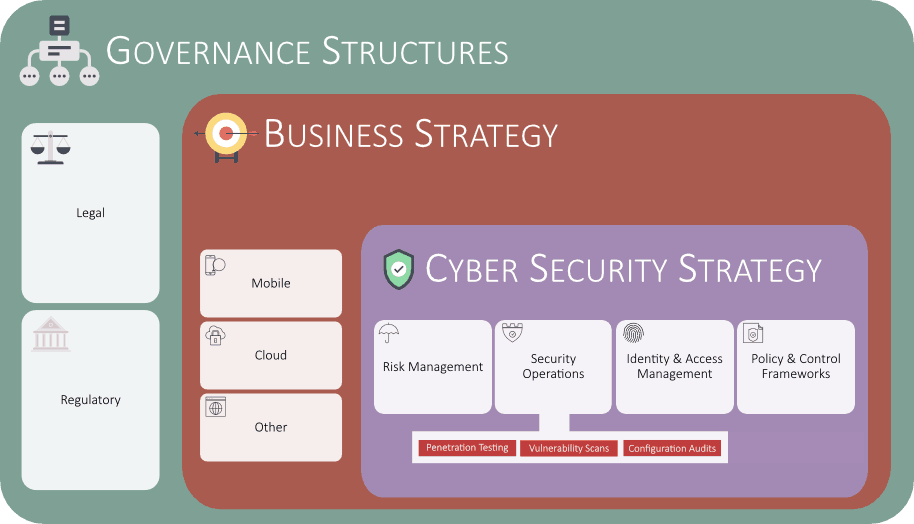
This paper focuses on three common testing types – vulnerability scanning, penetration testing and configuration audits. It is not a technical ‘how to’ explaining the test types and testing options. Instead it focuses on the benefits and limitations of each tool, and covers how they can be successfully integrated into business processes, common mistakes made and how to correct them. It covers aligning executive team expectations with what the tools can realistically do, how to use vulnerability scan reports (and how not to), what can and cannot be outsourced, and finally latest trends and technologies to look at.
The content will be most useful for organizations with a less mature information security infrastructure, especially small to medium enterprises (SMEs). Content is drawn from publicly available data sources as well as CipherQuest’s extensive work history in the Caribbean and EU regions. Possible target audiences are clients with limited or no in-house security skill sets, clients being mandated into compliance for legal or other business reasons, and clients with existing processes that are not fully meeting expectations.
